There have been a lot of changes around the world in 2020 with the pandemic, and walking into the year 2021 will not change a lot in terms of the new working style. A lot of industries have suffered a great deal, and they have learnt alternative ways to adapt and do their businesses.
Only a small percentage of companies took advantage of remote working and implemented such a solution before the pandemic compared to the current remote working proportion. Companies and government departments were on the fence about remote working and did not implement such solutions, especially on a large scale until their hands were tied to implement it in a short span of time. This is where the quick deployment of technology was vigorously tested to deploy a working environment for the people while maintaining the same level of collaboration and the effectiveness from a centralised office.
What about Security?
Even though we have gone from more of a centralised working model to a more diverse remote working environment. This has brought in its fair share of security problems. Even though these problems have been faced before the pandemic, but the mass deployment of remote working has made a tremendous impact on security.
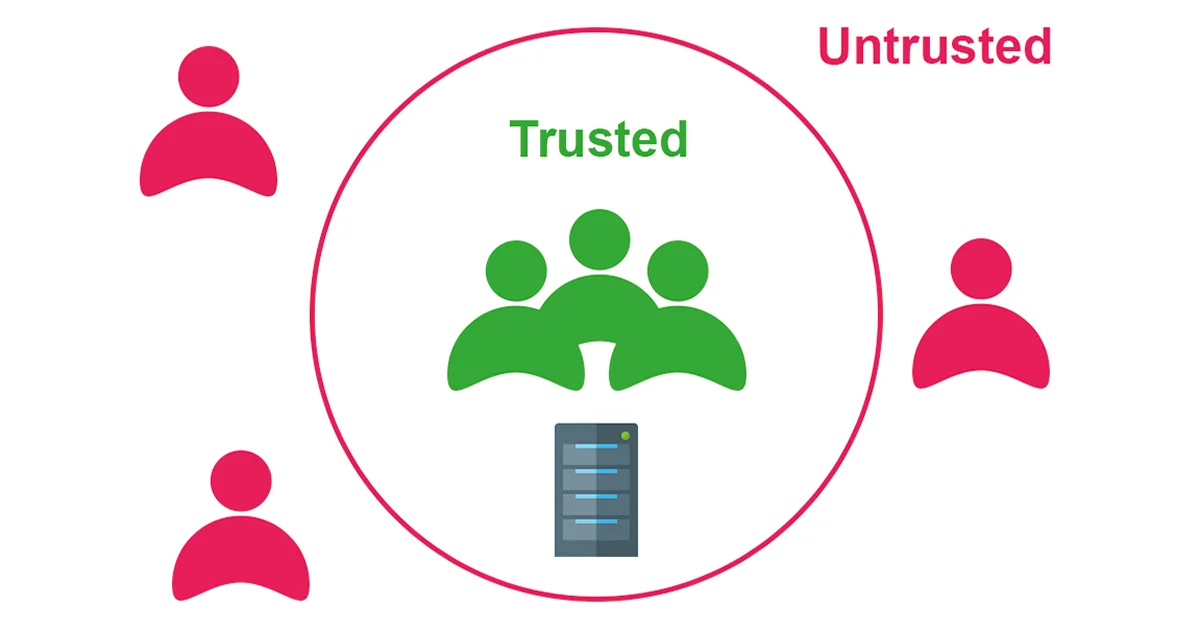
It is easier to control when all the users are in a centralised office where we could implement Perimeter Based Security. However, since staff are now working from home and joining meetings with people halfway around the world, the new remote working model is bringing in more security hurdles while delivering powerful business benefits. This has also made perimeter-based security even more untenable. It will give an attacker various other avenues to compromise a device and could easily slip through the defence.
Let’s look at the Problem
Perimeter-based security will work well when a company allows its staff to come into the office and use the provided workstations to perform their tasks. This will enable a company to deploy a security perimeter to protect all the information within the network in a particular location. This model worked very well until introducing remote working and BYOD deployment.
In terms of remote working, every single device is going to be coming from an external network into your infrastructure or in BYOD’s case, a device is going to have potential access to your internal network while having external connectivity to the outside world.
Security breaches happen when we overlook the more simple things and complicate the entire process itself. In another word, what makes security challenge is in fact when we over-complicate the design and its processes. One of the most overlooked security practices I have come across is the mobile devices and the BYOD policies of the company. It has been researched that a big proportionate of Android powered devices are running outdated and unpatched versions of operating systems, this potentially opens doors for an attack. However, if companies want to allow such devices, then they need to have a clear BYOD process in place to tackle this potential hole in the network. I will cover BYOD practices and policies in an upcoming article.
How do we tackle this problem?
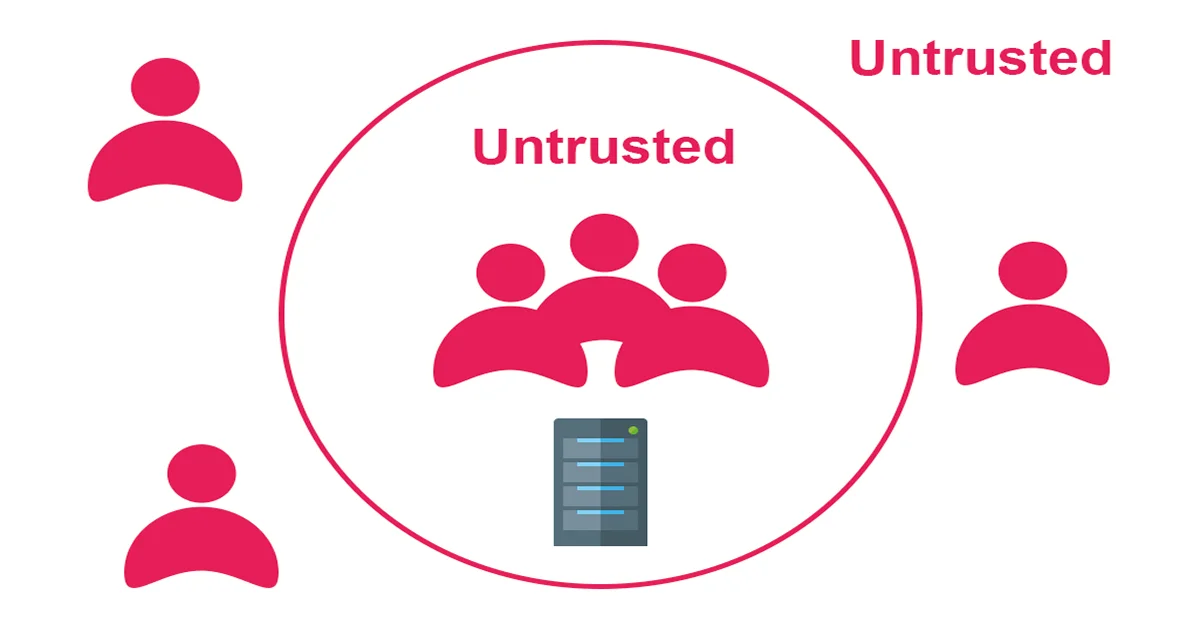
We are no longer able to trust a user by defining whether they are within or outside the perimeter of the defence. What we have to do is by adopting the zero-trust approach, whereby only trusted users and devices can access sensitive and restricted files and applications. The following model can be implemented to validate scenarios.
Wrong Credential + Wrong device = Access Denied
Correct Credential + Wrong device = Access Denied
Correct Credential + Correct device = Access Granted
The identity of the user can be further strengthened with the implementation of multi-factor authentication (MFA) where the Authentication is based on What they know (username & password) in conjunction with What they have usually either a security token, an SMS, a mobile device running a smartphone app to generate or to approve authentication requests.
The identity of the device can be authenticated by verifying the Certificate installed on to the device itself. This will also enable the company to maintain and patch the Operating System on the device free from vulnerabilities. In the case of a compromised device, the user will not be allowed access where the device will be quarantined and fixed the problem.
What is Zero Trust?
The Zero Trust model requires all the users in an organization regardless of their location to be authenticated, authorized, and continuously validated while being granted or keeping access to the end systems. This approach works hand in hand with multi-factor authentication and Identity Access Management (IAM) along with next-generation endpoint security technology to verify the user’s identity while maintaining system security.
How do we implement it?
When it comes to deploying a successful Zero Trust model in an organization we need to have the addresses of the following points.
Continuous monitoring of all the endpoints.
This is when we monitor all the endpoints which are being used to access the system. If such endpoint of compromised, it will be quarantined and denied access regardless of the user credential.
Contentious monitoring and validation of the users.
A user needs to be periodically validated while being granted to the system. This is to make sure the user is in fact who they say they are.
Continuous monitoring of the system.
This is an added benefit where we could monitor the end system for erroneous access. This can be achieved by the help of AI or any other method where for example if a user is accessing Data A & B for the past 6 months and if he suddenly goes and access Data X, then the system could flag for an audit. Other examples could be the amount of data transfer, the time they access the data etc.
Going one last mile
Even though the organizations can implement these changes, this does not guarantee the safety of their information systems. It is possible to implement access control models such as Role-based access control (RBAC), Mandatory access control (MAC) or they could implement both RBAC in conjunction with MAC.
And finally…
Information Security is a journey and not a destination. The points raised in this article are a guide, therefore it needs to be implemented with other aspects of things. If you need to discuss any low low-level design ideas, you are more than welcome to contact me.
