In the realm of choosing technology for your companies’ Cloud, SaaS, or IaaS solution providers, we often rely on a select few providers since they tend to meet most of our requirements. A classic example is Microsoft, being one of the most prominent players in the industry, which offers a range of services that have become crucial components for many organisations.
When a company has an on-premises Domain Controller, you might be looking at options such as Azure AD while exploring ideas to move Active Directory to the Cloud. While we look at Azure AD, we will come across offering such as Microsoft 365 E5 licensing. Microsoft 365 E5 is a cloud-based suite of Microsoft 365 productivity apps combined with advanced voice, analytics, security, and compliance services all into one suite. I have seen most companies choosing this option along with email Exchange and it is clearly a no-brainer when choosing these offerings.
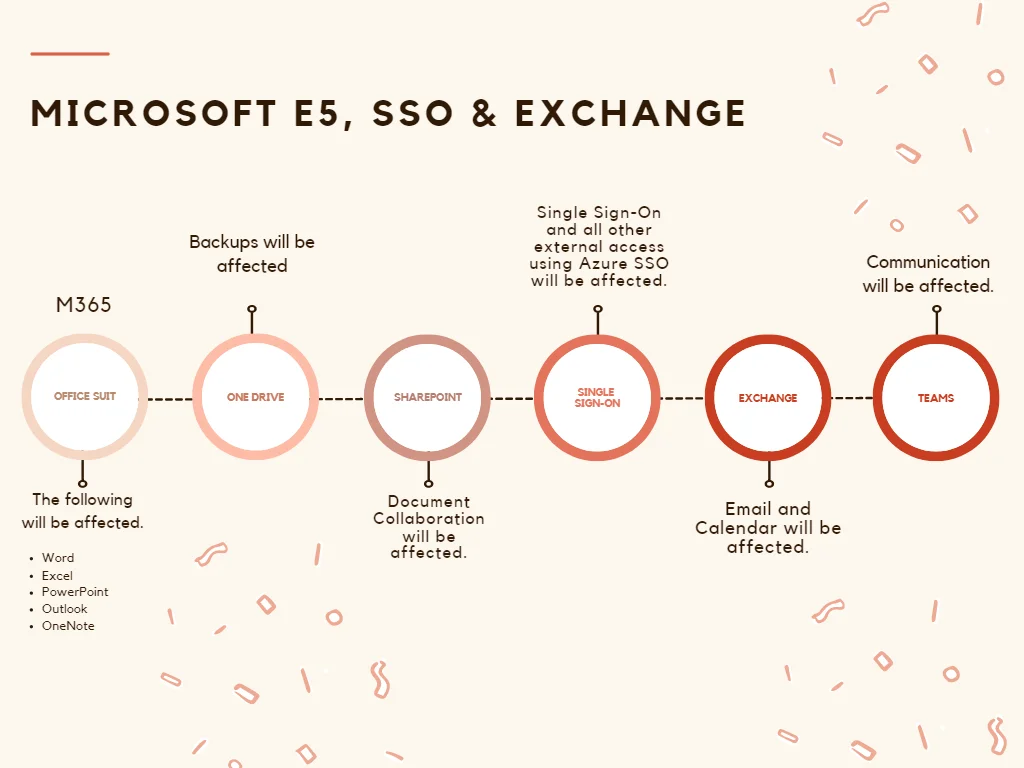
However, when organisations choose to put all their eggs in one basket, they are entrusting a single provider for critical services like Microsoft Azure Active Directory (AD), Exchange, SSO and Microsoft 365, they may inadvertently expose themselves to significant risks.
I will explore a few potential dangers of such an approach and provide insights through real-life examples.
1. Overdependence on a Single Provider:
When we solely rely on a single provider for essential services such as Email, SSO, Communication etc, the organisations become highly dependent on that provider’s stability, reliability, and security. This all boils down to the Availability of such services. In the case of Microsoft Azure AD, Microsoft SSO, Microsoft Teams, and Microsoft 365, organisations might face severe consequences if any disruptions occur, such as outages or security breaches. These incidents can lead to prolonged downtime, loss of productivity, and compromised data.
This could lead to an organisation could be left dead in the water in terms of connectivity. In a very extreme situation, If Availability and Communications are severed by an outage, the organisation will have no means to communicate or have any collaboration in place to function its business needs. Furthermore, the employees will be left in the dark and will not have any means to find out the cause of the outage nor they will have any information available in terms of the outage. In the event of such an issue, there is a chance that we may have to invoke the DRP.
A less severe example is…
On March 15, 2023, Microsoft experienced a major outage that affected Microsoft Azure AD services worldwide. This resulted in numerous organisations relying on Azure AD faced significant challenges, such as the inability to authenticate users, access critical data, and utilise various cloud-based applications.
On June 7, 2023, Microsoft has confirmed that recent outages to Azure, Outlook, and OneDrive web portals resulted from Layer 7 DDoS attacks against the company’s services. These incidents highlighted the vulnerability of relying on a single provider, emphasising the need for contingency plans and diversification.
2. Limited Flexibility and Customisation:
When organisations opt for a single-provider solution, they may find themselves constrained by the provider’s offerings and their limitations. When we look at each business, they have their own unique requirements, and relying solely on a single provider might limit the ability to fine-tune the solutions to specific needs. Even though it is more often seen as a trade-off, but lack of flexibility and customisation can hinder innovation, prevent optimisation, and stifle the organisation’s growth up to a certain level.
3. Security and Compliance Risks:
The ever-increasing prevalence of cyber threats, security and compliance have become critical concerns for organisations. When we rely on a single provider, organisations put themselves at a higher risk of being affected by a single point of failure. If the provider experiences a security breach, it can have devastating consequences for all the organisations relying on its services.
Example: In 2021, the SolarWinds cyberattack affected numerous organisations, including those relying on Microsoft 365. This incident exposed vulnerabilities in the supply chain and emphasised the importance of diversification and layered security measures.
Conclusion:
While I think Microsoft Azure, Microsoft 365, and similar services offer valuable solutions for organisations, it is essential to conduct a thorough risk analysis on these applications. One of the solutions is to diversify technology providers. Businesses can mitigate the risks associated with service disruptions, limited customisation, and security breaches. Embracing a multi-vendor or multi-cloud approach and implementing robust contingency plans can provide organisations with flexibility, resilience, and peace of mind.
An example could be running Okta with Azure Active Directory and Slack with Microsoft Teams. This will allow organisations to seamlessly integrate their identity and access management (IAM) solutions and collaboration platforms. The Okta integration with Azure AD will allow users to leverage single sign-on (SSO) capabilities and centralised user management across both platforms, enhancing user experience, streamlining access control. The Slack integration with Microsoft Teams will enable cross-platform communication and collaboration, allowing teams to work together seamlessly, regardless of their preferred platform. These integrations foster a unified and efficient workflow, ensuring secure access and efficient collaboration within the organisation. These integrations will allow a company to have a diverse provider architecture resulting in better risk management controls.
Remember, in the ever-changing landscape of technology, it is prudent to distribute your dependency to a certain level of providers to ensure a more secure and adaptable environment for your organisation’s success. On the other hand, the organisation could simply accept the risk and stick to a single provider if they meet their RTO/RPO.
